Your staff are probably already saving passwords in the browser.
It is fast. It feels harmless. And that is often exactly how a bad practice takes hold.
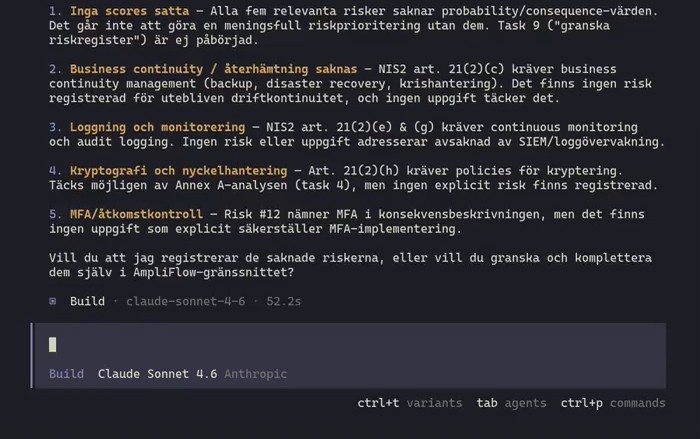
A widely shared video from Tom Jøran Sønstebyseter Rønning shows why this is worth taking seriously.1 The video shows a command window where saved passwords appear to be dumped from Microsoft Edge for multiple users. If saved passwords can be read out like this, the problem is not only technical. The same browser is often a shortcut into email, customer data, HR systems, finance, and internal tools.
Microsoft Edge loads all your saved passwords into memory in cleartext - even when you’re not using them.
— Tom Jøran Sønstebyseter Rønning (@L1v1ng0ffTh3L4N) May 4, 2026
The first question to ask is simple: could something similar happen here?
If the answer is “maybe”, you probably already have enough reason to act.
Executive overview
This is not just a Microsoft Edge issue, that is the browser. This is about how you handle passwords and other login details in the business.
When staff save passwords in the browser, you move a sensitive protection closer to everyday work, and further away from governance. When something goes wrong, the problem becomes bigger than the browser itself. It becomes access to email, customer data, HR, finance, and internal tools.
ISO 27001 does not literally say “do not save passwords in the browser”. But the standard does require that authentication information is managed in a controlled way, that access is restricted, that user devices are protected, that secure authentication is used, and that rules are followed up. A mature ISO 27001 approach would therefore likely have made this practice less common, less risky, and easier to detect.
My recommendation is simple: do not allow the browser to save passwords for business-critical accounts. Ideally, disable the feature for company accounts and use a dedicated password manager with clear governance, sharing, revocation, and strong authentication.
Start here
You do not need to wait for a large security project to reduce the risk.
Do this first:
- Decide which accounts must never be saved in the browser. Start with email, admin, HR, finance, CRM, and systems with personal data.
- Require stronger authentication for sensitive accounts. One saved password should not get an attacker very far.
- Review which users have too much access. The more an account can reach, the bigger the damage.
- Treat clients and browsers as security matters, not user preferences.
- Decide how you detect, report, and correct improper local storage of logins.
This does not solve everything. But it moves you away from relying on luck.
Why this becomes a business problem
Many people think about IT first. That is too narrow.
If a user’s browser gives access to email, an attacker can reset other passwords. If the same user has also saved logins to customer systems, supplier portals, or internal tools, one account becomes a path forward.
That is why this is not just about browsers. It is about how you handle passwords and other login details in the business.
The reason is rarely stupidity. The reason is convenience. People want to log in and move on. If the organization does not have clear rules, or if the rules are never followed up, convenience wins.
How ISO 27001 would have reduced the risk
ISO 27001 would not have made you invulnerable. But good work under the standard would have done three things:
- reduced the chance that sensitive passwords are stored in the wrong place
- limited the damage if something still leaks
- made you faster at detecting and correcting the problem
In practice, that comes from four things.
1. You would have had to decide what is sensitive
The standard requires you to assess information security risks and classify information.2
In practice, that means you cannot treat all accounts as equal. A newsletter tool account is not the same as the CEO’s email or your HR system. Once you classify the information, the next question becomes natural: which logins are allowed to be saved in the browser at all?
2. You would have had to govern authentication information
The clearest wording sits in Annex A 5.17:
Allocation and management of authentication information shall be controlled by a management process, including advising personnel on appropriate handling of authentication information.
- ISO/IEC 27001:2023, Annex A 5.17
Together with rules for acceptable use, identity management, and access control, that means password handling cannot be left to personal habit.3
That leads to real decisions, such as which accounts must never be saved locally, which roles need stronger authentication, and who may approve exceptions.
3. You would have had to protect user devices better
Annex A requires that information stored on or accessible via user devices is protected. It also requires controlled security configurations and management of technical vulnerabilities.4
That is directly relevant to browsers. If you do not control whether passwords may be stored locally, which extensions may run, or how quickly clients are updated, you leave an unnecessary hole open.
4. You would have limited the damage and learned faster
Good security work does not only try to stop problems. It also limits damage when something still happens.
That is why access control, secure authentication, logging, incident handling, and regular follow-up matter here.5
If you have a rule that sensitive accounts must not be saved in the browser, but never check compliance, then in practice you do not have a rule at all.
When does ISO 27001 become truly relevant?
ISO 27001 becomes truly relevant when these questions keep returning, and each time are solved ad hoc.
When nobody knows which accounts are saved locally. When rules exist, but nobody follows them up. When client protection, access control, training, and incident learning live in separate boxes.
That is when a management system becomes interesting. Not as administration. As a way to get control.
If you recognize yourselves in this, it is reasonable to ask whether the time has come to take ISO 27001 seriously, or to go all the way to certification. Not because the standard literally bans saved browser passwords. Because it forces you to stop leaving decisions like this to chance.
Footnotes
-
Tom Jøran Sønstebyseter Rønning, post on X, 4 May 2026. Verified text and URL: https://x.com/i/status/2051308329880719730. ↩
-
ISO/IEC 27001:2023, clause 6.1.2 and Annex A 5.12, local source in the standards collection. ↩
-
ISO/IEC 27001:2023, Annex A 5.10, 5.15, 5.16, and 5.17, local source in the standards collection. ↩
-
ISO/IEC 27001:2023, Annex A 8.1, 8.8, and 8.9, local source in the standards collection. ↩
-
ISO/IEC 27001:2023, Annex A 8.3, 8.5, 8.15, 8.16, and 5.24, 5.25, 5.26, 5.27, and 5.36, local source in the standards collection. ↩