Build an ISMS that works in daily operations. Risks, controls, SoA, tasks and follow-up in one platform, from your first gap analysis to certification.
ISO 27001 gets strong when information security does not live in separate documents, but in the work your team already does. AmpliFlow helps you connect ownership, risk work, control status and improvements so your team and your auditor see the same reality.
Where do you stand against ISO 27001 today?
Get a clear picture of your current information security maturity - free and no commitment. Answer 12 clause-by-clause questions and receive concrete recommendations on what needs strengthening.
Gap Analysis: Where do you stand against ISO 27001?
Answer 12 questions and get an assessment of your current state - plus concrete tips on what you need to do to reach certification.
From smaller teams with customer requirements to larger companies with multiple standards. AmpliFlow fits organizations that want to work in one system, not collect evidence in five.





Three words. The entire foundation.
Confidentiality, integrity and availability. All information security work revolves around protecting these three. AmpliFlow helps with all of them.
Confidentiality
Right person, right information. Nobody else.
- Access control
- Encryption
- Classification
Integrity
Information is accurate and untampered. Every change is tracked.
- Audit trail
- Access control
- Traceability
Availability
Systems work when needed. Not "soon", but now.
- Redundancy
- Backup
- Incident management
93 controls. Organized, not overwhelming.
ISO 27001:2022 defines 93 controls across 4 themes. Click through them and see what each control actually means. AmpliFlow has all 93 controls built in with AI assistance for generating content, automatic SoA, and task management per control. Learn more about control management →
Explore Annex A
93 controls. Click a theme to explore.
93 controls sounds overwhelming. AmpliFlow has all of them built in with AI assistance, automatic SoA, tasks, and status tracking per control.
Why more teams prioritize ISO 27001 now
The drivers are not only threats. They are about showing control, working with less friction and answering customers and partners faster.
The Cybersecurity Act reshapes buyer expectations
The Cybersecurity Act makes leadership, accountability, risk management and follow-up part of normal business governance. Teams with a working ISMS respond faster to customers, audits and procurement reviews.
Cyber Resilience Act
If you build software or connected products, you need to show how security work, changes and ownership fit together. ISO 27001 gives you the structure, AmpliFlow makes the work visible day to day.
Defence supply chains
Defence, critical infrastructure and larger industrial buyers want to see working governance, not only policy documents. A living ISMS makes you easier to assess and easier to choose.
Small teams need workable routines
Threats are real, but small and mid-sized companies often get stuck in manual work, scattered spreadsheets and unclear ownership. You need a system for running the work, not a side project for maintaining documentation.
Your supply chain is an attack surface
Customers and partners do not only assess your technology. They assess how you follow up suppliers, access, incidents and changes. That needs to be visible without gathering evidence at the last minute.
Customer requirements cascade
The question is rarely only whether you have a certificate. The question is whether you control risks, controls, nonconformities and ownership. When the work already lives in the platform, the answer is easier to show.
From asset to action
ISO 27001 requires risk-based thinking. AmpliFlow makes it concrete in daily work: link risks to assets, assess them systematically and follow actions until they are actually done.
Living risk register
Link risks to assets, threats and vulnerabilities. See what waits for a decision, what is already being treated and what risks are starting to drift.
Statement of Applicability
Track all 93 controls with justifications, owners and implementation status. The SoA becomes a working tool, not a document you only open before an audit.
Consolidated risk picture
Link risks to processes, assets, projects and actions. That makes prioritisation easier when everything cannot be done at once.
Centralized documentation
Policies, procedures, decisions and risk assessments live in the same flow. Auditors find the evidence quickly, and the team knows what applies in daily work.
Certification gets easier when the work already happens in the platform
ISO 27001 is not only about describing ways of working. It is about risks being assessed, controls being followed up, nonconformities being closed and leadership seeing the real status. AmpliFlow is where that work happens.
Projects and security goals
Security improvements, goals and follow-up live in the same system as your ISMS. Link controls to outcomes, owners and deadlines so the work keeps moving.
Processes and competence
Security processes are linked to the people who need to follow them. Competence, training and accountability stay in the same workflow as the rest of the ISMS work.
Nonconformities that drive improvement
Every security incident and nonconformity leads to root cause analysis, action and verification. Improvement work happens inside the system, not after the fact around it.
AI support for control work
AI helps fill control explanations, SoA text and working drafts without losing traceability. It saves time, but ownership of the controls stays with your team.
Learn about control management →One platform for multiple standards
Add ISO 9001, 14001 or 42001 and you build on the same foundation. Shared processes, nonconformities and accountability reduce duplicate work.
Read about integrated management systems →Start with the right level of support
Mini fits teams that want to run more of the ISMS work themselves. We set up the environment, base structure and working model so you can continue in AmpliFlow without starting from an empty system.
Questions about ISO 27001
Straight answers about certification, working methods and platform support.
What is the Statement of Applicability (SoA)?
The SoA lists all 93 controls in Annex A and documents which ones apply to your scope, why, how they are handled and how you show that. It is one of the most important audit inputs, but it is also what helps the team keep the daily work connected.
Do we need to implement all 93 controls?
No. You must consider all of them but can exclude those not relevant to your scope and risk profile. Each exclusion must be justified. A physical server room control isn't relevant if you only use cloud services, for example.
How does ISO 27001 relate to NIS2 and the Cybersecurity Act?
The Cybersecurity Act requires structured work with risks, incidents, accountability and follow-up. ISO 27001 gives you an established management system for that work. Many organizations therefore use ISO 27001 as the practical backbone of their NIS2 and Cybersecurity Act effort.
How long does certification take?
It depends on size, maturity and how much already works in daily operations. Gap analysis and risk assessment usually move faster than getting ownership, controls, training and follow-up to stick. The auditor wants to see that the system is used, not only described.
What does certification cost?
The total cost includes implementation, certification audit and ongoing maintenance. Internal time is usually the biggest part. That is why it pays to keep risks, controls, documents and actions in one system the team actually uses, instead of building the whole setup around spreadsheets and folders.
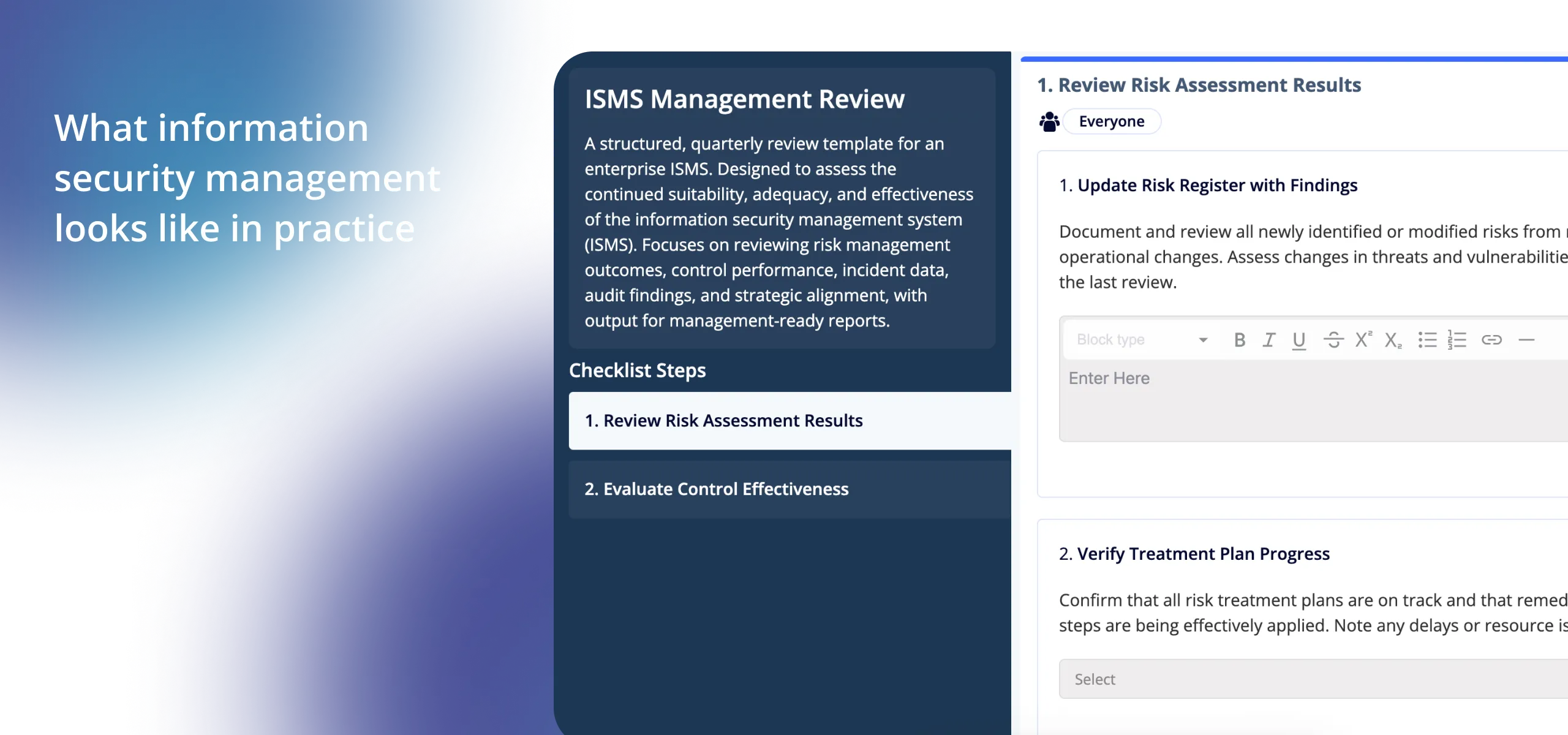
Ready to build an ISMS that works in practice?
Book a demo and we will show you how AmpliFlow brings risks, controls, SoA, actions and follow-up into one workflow your team can actually use. Practical focus, not sales talk.